The difference really boils down to this: your public key is a lot like your home address. You can share it with anyone who needs to send you something. Your private key, on the other hand, is the only key that opens your front door to get what's inside.
It's not about choosing one or the other. They're a perfectly matched pair, designed to work in tandem.
Understanding the Core Concepts
To really get the dynamic between a public and private key, you have to see them as two sides of the same cryptographic coin. This system, known as asymmetric cryptography, links them mathematically but gives them opposite jobs. One is meant for sharing far and wide, while the other is guarded with absolute secrecy.
This ingenious pairing is what creates a secure digital identity, enabling safe transactions and communications across the internet. The entire security model hinges on a brilliantly simple principle: what one key locks, only its unique partner can unlock.
This relationship ensures that even if everyone on the planet knows your public key, your private assets and data are safe—as long as you alone control the private key. For anyone getting into crypto, this isn't just a detail; it's the bedrock. If you want to build on this, the VTrader Academy has a ton of great resources to expand your knowledge.
Key Characteristics at a Glance
Let's break down their core traits.
- Public Key: Designed for distribution. Think of it as your bank account number. You share it freely so people can send you money, but no one can use it to take money out.
- Private Key: Must be kept secret, always. It's your digital signature and the ultimate proof that your assets belong to you. If it gets out, your security is shattered.
- Mathematical Link: The keys are generated together as a unique pair. It's computationally impossible to reverse-engineer a private key just by having its public counterpart.
The core takeaway is simple: your public key is for receiving, and your private key is for signing or spending. Protecting your private key is the single most important responsibility in managing digital assets.
Quick Comparison Public Key vs Private Key
To make things even clearer, here’s a quick side-by-side look at how these two keys stack up.
| Attribute | Public Key | Private Key |
|---|---|---|
| Purpose | To receive encrypted data or cryptocurrency. | To decrypt data and authorize transactions. |
| Distribution | Shared openly with anyone. | Must be kept completely secret. |
| Analogy | A public mailbox address or bank account number. | The physical key to your mailbox or your bank PIN. |
| Primary Use | Encryption and signature verification. | Decryption and digital signing. |
This table lays out the fundamental separation of duties. One is your public-facing receiver, and the other is your private, all-powerful authenticator.
How Asymmetric Cryptography Secures Communication

To really get the whole public key vs private key relationship, you first need to grasp the brilliant system they enable: asymmetric cryptography. This approach solves a massive security problem that plagued older methods—it gets rid of the need to share a secret key to communicate securely.
Think of it like this: you want to send a locked box to a friend. With old-school symmetric cryptography, you'd have to send the physical key separately, praying no one grabs it along the way. Asymmetric cryptography is a game-changer because it creates two different but mathematically connected keys right from the start.
This mathematical link is the secret sauce. Your public key, just like the name says, is for sharing with anyone and everyone. The private key, on the other hand, is yours alone. Keep it secret, keep it safe. This setup creates a powerful one-way security function.
The Encryption and Decryption Flow
The process itself is surprisingly straightforward. When someone wants to send you a secure message, they use your public key to encrypt it. Imagine them placing their message in a special lockbox that only your unique, private key can ever open.
Once that message is locked up (encrypted), it's just gibberish to anyone who might intercept it. Even the person who sent it can't open it back up.
The only thing on earth that can unlock that message is your private key. This is what guarantees confidentiality. The key that locks the data is totally different from the key that unlocks it.
This one-way relationship is the absolute foundation of digital trust. It ensures that only the intended recipient—the one person holding the private key—can ever read the encrypted information.
It’s no surprise that reliance on this technology is exploding. The global Public Key Infrastructure (PKI) market, which is the framework supporting all this, was valued at around USD 6.37 billion in 2024. Projections show it rocketing to nearly USD 19.65 billion by 2030, a clear sign of the intense demand for secure digital interactions.
More Than Just Secret Messages
This isn't just for spy movie-style communications; it's the bedrock of modern internet security. Every time you see that little padlock icon in your browser's address bar, you're watching asymmetric cryptography work its magic to secure your connection.
It's also absolutely essential in the world of cryptocurrency.
- Receiving Funds: Your public key is your wallet address. You can share it freely with anyone who wants to send you crypto.
- Sending Funds: To authorize a transaction and prove you actually own the funds, you must sign it with your private key.
If you lose your private key, you lose your crypto. Forever. That's why keeping it secure is non-negotiable. For more on managing crypto assets safely, you can dig into the common questions we answer in our detailed vTrader FAQ. This fundamental process of signing and verifying is what keeps countless digital interactions honest and secure.
A Functional Breakdown of Each Key's Role
To really get a handle on the elegant dance between public and private keys, you have to look past the simple definitions and dig into their specific jobs. Each key has a distinct, non-overlapping role in the functions that keep our digital lives secure. They’re like a specialized team where one partner handles a task the other is explicitly designed not to do.
This clear separation of duties is what builds trust in everything from secure messaging apps to cryptocurrency transactions. Let's break down exactly what each key is doing during encryption, decryption, signing, and verification.
Functional Analysis Public Key vs Private Key
To see the division of labor clearly, it helps to put their roles side-by-side. Each key has a very specific, complementary purpose that makes the whole system work.
| Function/Characteristic | Role of Public Key | Role of Private Key | Real-World Analogy |
|---|---|---|---|
| Primary Purpose | To encrypt data and verify signatures. It's the "public" face. | To decrypt data and create digital signatures. It's the "secret" key. | A secure mailbox slot vs. the unique key that opens the mailbox. |
| Distribution | Shared freely and openly with anyone. | Kept completely secret and never shared. | Your home address (public) vs. your front door key (private). |
| Encryption | Used by others to "lock" a message intended only for you. | Cannot encrypt data. Its job is to unlock, not lock. | Anyone can drop a letter in your mailbox slot. |
| Decryption | Cannot decrypt messages. It only works one way—for locking. | The only key capable of "unlocking" messages encrypted with its public pair. | Only you have the key to open the mailbox and read the letters. |
| Digital Signature | Used to verify that a signature is authentic. | Used to create a unique, legally-binding digital signature. | The post office verifying the sender's stamp vs. you signing a check. |
| Generation | Derived from the private key in a one-way mathematical process. | Generated first, from which the public key is then created. | A copy of a key that can only lock, not unlock. |
This table highlights the core principle: what one key does, the other cannot. This intentional asymmetry is the entire foundation of public-key cryptography.
Encryption The Role of the Public Key
Encryption is just the process of scrambling a message so that only the right person can read it. In this scenario, the public key is the lock. Anyone who wants to send you something securely uses your publicly available key to encrypt their message.
Think of it like a high-security mailbox slot. Anyone can slide a letter through it, but once it's inside, it’s sealed shut. The process is strictly one-way; the same public key used to lock the data can’t be used to unlock it.
This is where the private key steps in as the guardian of your digital assets.
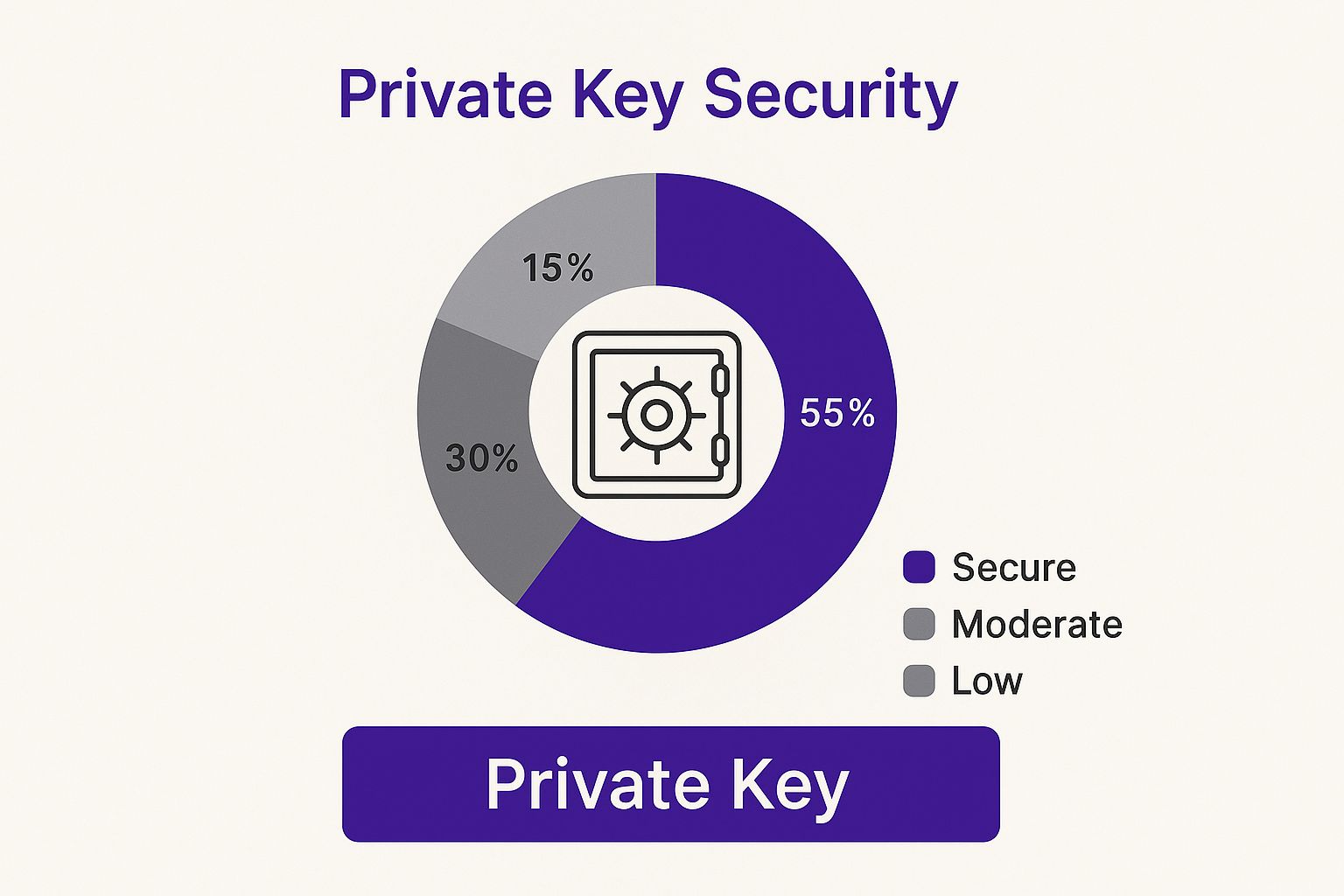
This visual drives home the point: while the public key is for receiving encrypted information, the private key is the ultimate gatekeeper, protecting and granting access.
Decryption The Role of the Private Key
After a message is encrypted, decryption is simply the act of unscrambling it back into a readable format. This is where the private key acts as the unique key to unlock the data. It is literally the only thing in the world that can reverse the encryption performed by its public counterpart.
If someone locks a file with your public key, only your private key can decrypt it. This guarantees total confidentiality. Not even the original sender can get back into the encrypted information without access to your private key.
Digital Signatures The Role of the Private Key
Cryptography isn't just about secrecy; it's also about authentication—proving you are who you claim to be. A digital signature is a tamper-proof seal, and creating one is a job exclusively for the private key. When you authorize a crypto transaction, for instance, your wallet uses your private key to "sign" it.
This signature is a unique cryptographic hash of the transaction data, generated with your secret key. It’s undeniable proof that you, and only you, approved the action. It's crucial to understand your responsibilities here; for more on user obligations, you can see the vTrader terms and conditions.
Signature Verification The Role of the Public Key
So, how does anyone know your digital signature is legit? This is where the public key comes back into play. Anyone can use your public key to verify the signature that your private key created.
When a recipient's system gets your signed message, it uses your public key to run a check. If it all matches up, it confirms two critical things:
- Authenticity: The message was definitely signed by the owner of the corresponding private key.
- Integrity: The message hasn't been changed one bit since it was signed.
This verification completes the security loop. The public key confirms the proof of identity that only the private key could have created in the first place.
Practical Use Cases in Crypto and Online Security
All the theory behind public and private keys really clicks when you see them working behind the scenes in your everyday digital life. This cryptographic duo is the silent guardian securing everything from your crypto portfolio to your casual web browsing.
Nowhere is this more obvious than in the world of cryptocurrency. In this arena, the difference between the two keys has immediate and serious financial consequences.
Your public key is essentially your wallet's receiving address. Think of it like your personal bank account number on the blockchain. It's generated from your private key, and you can share it with anyone who wants to send you crypto like Bitcoin or Ethereum without a second thought.
Your private key, on the other hand, is the master key that authorizes every single outgoing transaction. When you decide to send funds, your wallet uses this key to create a digital signature, proving you're the rightful owner and giving the green light for the transfer. If you lose this key, your funds are gone for good.
Securing Your Web Browsing with SSL and TLS
Ever notice that little padlock and "https://" in your browser's address bar? That's public key cryptography in action. Protocols like Secure Sockets Layer (SSL) and its modern successor, Transport Layer Security (TLS), are what create a secure, encrypted link between you and the websites you visit.
Here’s a quick rundown of how it works:
- Your browser connects to a website and asks for its SSL/TLS certificate, which contains the site's public key.
- After verifying the certificate is legit, your browser uses that public key to encrypt a brand-new, one-time session key.
- It sends this encrypted session key back to the website's server.
- The server then uses its private key—and only its private key—to decrypt the session key.
With that handshake complete, both your browser and the server now share a secret key to encrypt all communication for the rest of your visit. It’s a brilliant system that keeps prying eyes away from your data, all made possible by the interplay of the public key vs private key.
This entire process creates a trusted, private tunnel over the inherently public internet. The public key kicks things off, but only the server's private key can seal the deal and unlock the secure channel.
Protecting Privacy with Email Encryption
Public key cryptography is also a game-changer for keeping private conversations, like emails, truly private. Tools that use Pretty Good Privacy (PGP) and similar standards let you scramble messages so that only the person you're sending them to can ever read them.
To send a secure email, you encrypt your message using the recipient’s public key. That email is now just a jumble of unreadable code to anyone who might intercept it—even your email provider. Only the intended recipient, who holds the matching private key, can decrypt and read it. This is a core principle of digital confidentiality, something we take very seriously. You can review our vTrader privacy policy for more on how we're committed to protecting user data.
These examples are just the tip of the iceberg. This technology also underpins software authentication, secure remote server access (SSH), and much more. For a deeper dive into the terms shaping this space, a good Web3 Dictionary can be an invaluable resource.
Best Practices for Key Security and Management

Getting a grip on the mechanics of public vs. private keys is one thing. Actually protecting them is where the real work begins, especially when it comes to your private key. The fallout from a compromised private key is swift, severe, and almost always permanent—think total loss of your crypto assets or a catastrophic data breach.
There’s one golden rule, and it’s non-negotiable: never, ever share your private key. Treat it with the same secrecy as the master key to your entire life. Slapping it online, shooting it over in an email, or saving it on a public computer is just asking for trouble.
Fortifying Your Private Key Storage
The single most effective way to protect your private key is to get it offline. Any device connected to the internet is a potential attack vector. This strategy is known as "cold storage," and it’s the gold standard for anyone serious about security.
Here are the most battle-tested methods:
- Hardware Wallets: These are physical devices, usually looking like a USB stick, built for one purpose: storing your private keys offline. When you need to sign a transaction, it happens right on the device, meaning your key is never exposed to your computer or the internet.
- Paper Wallets: This old-school method involves printing your private key—often as a QR code—on paper and locking it away somewhere safe, like a fireproof safe. It works, but you have to worry about physical damage, loss, or theft.
- Air-Gapped Computers: For the truly paranoid (or truly wealthy), some users set up a dedicated computer that never connects to the internet. This machine is used exclusively for key management and signing transactions, offering a powerful layer of isolation.
To dive deeper into protecting the master key that generates all your private keys, check out this ultimate seed phrase security guide.
Advanced Security for Organizations
When you’re talking about a business or institution managing millions in assets or highly sensitive data, consumer-grade wallets just don’t cut it. This is where professional-grade hardware enters the picture, and the industry is taking notice.
Hardware Security Modules (HSMs) are specialized, tamper-resistant devices built to securely generate, store, and manage cryptographic keys. Their growing adoption shows just how seriously large organizations are taking the threat of private key theft.
The perceived importance of HSMs in encryption and key management programs more than doubled in just five years, jumping from 33% in 2015 to 66% by 2020, according to a global survey of IT security professionals. This isn't just a minor uptick; it's a clear signal that enterprises see robust hardware as essential for locking down their keys.
Of course, hardware is only part of the puzzle. Strong internal policies are crucial. Organizations should be enforcing regular key rotation schedules, setting up multi-signature protocols that require multiple approvals for a transaction, and running frequent security audits. This layered defense helps eliminate single points of failure. As our vTrader refund policy notes, users ultimately bear the responsibility for securing their own access credentials.
Common Questions About Public and Private Keys
As you get more familiar with the crypto space, a few key questions about public and private keys always seem to pop up. Getting a handle on these is make-or-break for keeping your digital assets and communications safe. Let's dig into some of the most common concerns newcomers have.
What you'll find is that a huge amount of responsibility falls squarely on your shoulders to keep your cryptographic secrets locked down.
What Happens if I Lose My Private Key
Losing your private key is, for all intents and purposes, a total disaster with no undo button. It’s like dropping the only key to a physical vault full of gold bars into the ocean. Once it's gone, it's gone. No locksmith on Earth can forge you a new one.
This means you are permanently locked out of anything that key secured. For crypto holders, this is the ultimate nightmare. If you lose the private key to your wallet, those assets are gone—forever. They're still on the blockchain, but completely inaccessible to you or anyone else.
This is why creating secure, offline backups of your private key or seed phrase isn't just a friendly tip—it's an absolute must for anyone serious about managing their own assets.
The whole point of self-custody is that you, and only you, are in control. The flip side is that you, and only you, bear the responsibility. There’s no "forgot my password" link when your private key vanishes.
Can You Get a Private Key from a Public Key
The answer here is a hard no. The entire security model of asymmetric cryptography crumbles if you could. It's built on the mathematical impossibility of working backward from a public key to find its private counterpart. That’s what makes the system trustworthy in the first place.
The two keys are mathematically connected, but it's strictly a one-way street. It’s incredibly simple to generate a public key from a private one. But trying to reverse the process would take an absurd amount of computing power—more than every computer on the planet combined—and trillions of years to crack.
This one-way design is crucial. It lets you share your public key with anyone without ever risking the secret that actually signs your transactions and unlocks your funds.
How Are Public and Private Keys Generated
Key pairs aren't just random bits of text; they’re the product of some seriously complex cryptographic algorithms. The whole process hinges on a blend of high-level math and a source of true randomness to make sure every single key pair is unique.
Here’s a simplified look at how it works:
- Gathering Randomness: The system first collects random data, known as entropy. This can come from anything from your mouse movements and keyboard strokes to system noise. This initial blob of randomness is called a seed.
- Applying the Algorithm: The seed is then plugged into a cryptographic algorithm. In the old days, it was often RSA (Rivest-Shamir-Adleman), but modern crypto almost exclusively uses ECC (Elliptic Curve Cryptography).
- Creating the Key Pair: The algorithm takes the seed and runs it through a series of intense calculations, ultimately spitting out a unique, mathematically linked private and public key.
The result is a key pair that's statistically impossible for anyone to guess or duplicate, giving us the strong foundation we need for secure digital finance. The math is so robust that the odds of two people generating the same key pair are practically zero.
Ready to put your knowledge into practice in a secure, zero-fee environment? Join vTrader today and start trading cryptocurrencies with confidence. Sign up now and receive a $10 bonus to kickstart your portfolio. https://www.vtrader.io

Steve Gregory is a lawyer in the United States who specializes in licensing for cryptocurrency companies and products. Steve began his career as an attorney in 2015 but made the switch to working in cryptocurrency full time shortly after joining the original team at Gemini Trust Company, an early cryptocurrency exchange based in New York City. Steve then joined CEX.io and was able to launch their regulated US-based cryptocurrency. Steve then went on to become the CEO at currency.com when he ran for four years and was able to lead currency.com to being fully acquired in 2025.




